Ahmed A. Omer, head of CX, e& enterprise, discusses how delivering exceptional customer experiences (CX) has become a paramount goal …


Ahmed A. Omer, head of CX, e& enterprise, discusses how delivering exceptional customer experiences (CX) has become a paramount goal …

Yarob Sakhnini, Vice President, Emerging Markets – EMEA at Juniper Networks says given AI’s capacity to enhance business operations and …
Cisco, the leader in security and networking, has unveiled a radically new approach to securing data centers and clouds in …

Mohammad Al-Jallad, CTO & Director, UKIMEA, HPE, discusses the trend of data hoarding and how factors such as cost, viability and accessibility might hamper the value such data can provide to enterprises.

Cloudflare Channel and Alliance Business Revenue Accelerates 174% Over Two Years and Expands with Additional Paths to Revenue, Program Awarded 5-Stars by CRN.

CEQUENS and stc Kuwait are confident that their collaboration will set new benchmarks in the telecommunications industry, providing businesses with the tools they need to thrive in an increasingly digital landscape.

Terry Young, Director of Service Provider Product Marketing, A10 Networks explores the most pressing attack vector for organisations to be aware of in the coming months.

Mohammad Al-Jallad CTO & Director, UKIMEA, HPE, outlines the value of cloud experiences as well as their costs in this exclusive op-ed for tahawultech which sets up the potential of the HPE GreenLake hybrid cloud platform.

CNME Editor Mark Forker spoke to Garsen Naidu, Director, Architecture specialists at Cisco Middle East and Africa, to learn more …

Moderated by Amit Ray, Managing Director, Protiviti Member Firm for the Middle East, the discussion exhorted businesses to foster a …

New program provides an “easy button” with Confluent’s partner ecosystem to augment teams, fund migrations and expedite data streaming journeys.

By adopting a comprehensive cybersecurity strategy, financial institutions can effectively protect their systems, safeguard sensitive customer data, and maintain their …

Investment Fuels Customer Success and Support, Product Innovation, and Growth as Endpoint Management Category Further Embraces Automation.

Manfred Felsberg, senior director, global data center business, Juniper Networks discusses how a paradigm shift towards automation, AI/ML-driven analytics and …

Evolving Product/Service Portfolio Ensures Agility, Performance, Reliability and Future-Readiness in Structured Cabling Environments.

Ericsson committed to reduce absolute scope 1, 2 and 3 greenhouse gas emissions by 90 percent between 2020 levels and the end of 2040.

Mohammad Wahba, Director, Systems Engineering – Middle East at Nutanix, has penned an exclusive op-ed which examines the cost dilemma …

CNME Editor Mark Forker spoke to Saud Al Akili, Head of Customer Support at stc Kuwait, to find out how …

CNME Editor Mark Forker managed to secure an exclusive interview with Hassan Allahham – Service Director, GCG Enterprise Solutions, who …
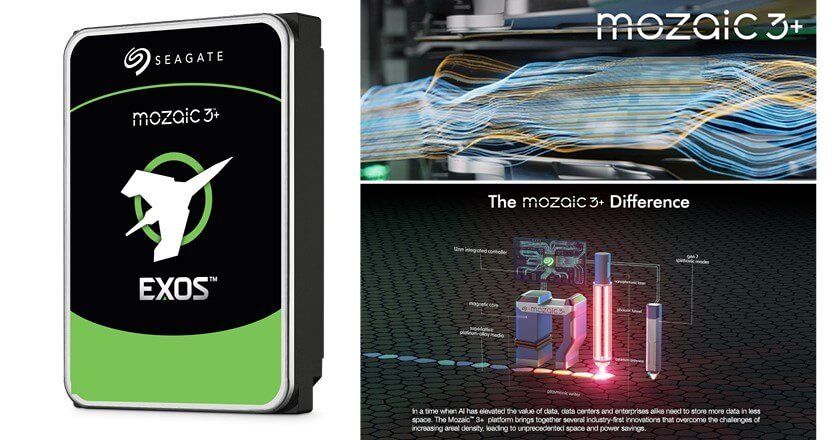
Seagate Technology Holdings, a world leader in sustainable mass-data storage solutions, has announced a milestone that marks a new era …