Service providers will benefit from Nokia’s focused development and leadership in future-ready core network software together with Red Hat’s deployment options for bare-metal, virtualised and public cloud.


Service providers will benefit from Nokia’s focused development and leadership in future-ready core network software together with Red Hat’s deployment options for bare-metal, virtualised and public cloud.
A series of malicious actions allow the extension to run stealthily while the user is browsing the internet. As a result, threat actors become capable of transferring the BTC from the victim’s wallet to their wallet using web injections.

Following the report on the Operation Triangulation campaign targeting iOS devices, Kaspersky researchers have released a special ‘trianglecheck’ utility that …
At the beginning of 2023 the share of users attacked with spyware in the Middle East increased by 11.8% from …

At its annual Think conference, IBM (NYSE: IBM) unveiled IBM watsonx, a new AI and data platform that will soon …

Company Marks a Decade of Participation at the Premier Security Event This Year.

Sujoy Banerjee, Associate Director, Sales & Business Development-UAE at ManageEngine, on why GISEC is an important platform to discover the latest security trends and how ManageEngine helps businesses stay ahead of the rapidly evolving and complicated threat landscape.

Accelerating recurring revenue to 80% of total revenue, with greater than 25% YoY ARR and 90% YoY subscription ARR growth.

SAP and Red Hat extend support for the RISE with SAP solution on Red Hat Enterprise Linux, the preferred operating system for net new business for RISE with SAP solution deployments.

Types of Ransomware Attacks and Cyber-Hygiene Best Practices.
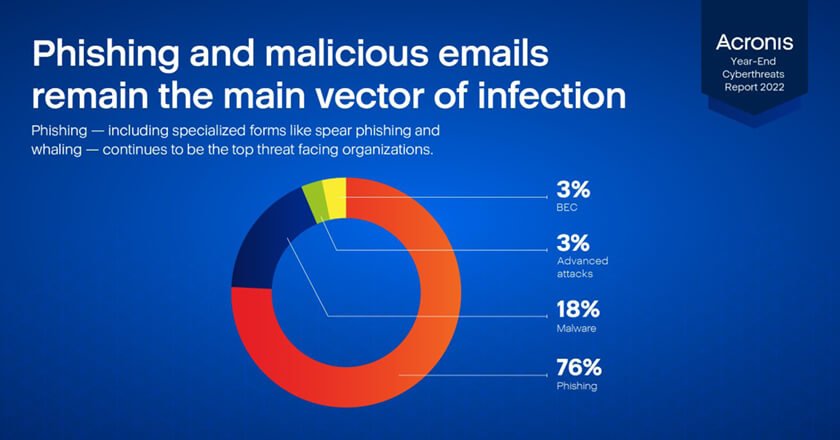
UAE organisations lost over 5.1M AED in ransomware in 2022 – Acronis Cyber Threat and trend report.

Sophos 2023 Threat Report: Criminals “Follow the Money” by Commercialising Cybercrime, Launching More “Innovative” Ransomware Attacks and Doubling Down on Credential Theft.

ESET launches APT activity report highlighting activities of Russia, North Korea, Iran and China-aligned threat actors, including attacks on aerospace and defence industries.

Tenable Announces New Research Alliance Program for Vulnerability Intelligence Sharing.

Intel Accelerates Developer Innovation with Open, Software-First Approach. Intel puts turnkey solutions into developers’ hands for AI, security, quantum computing and more.

How to manage IT infrastructure in a fast-growing company: the DataRobot experience.

Amr Alashaal, Regional Vice President – Middle East at A10 Networks, highlights the security ramifications and impact that Log4j is …
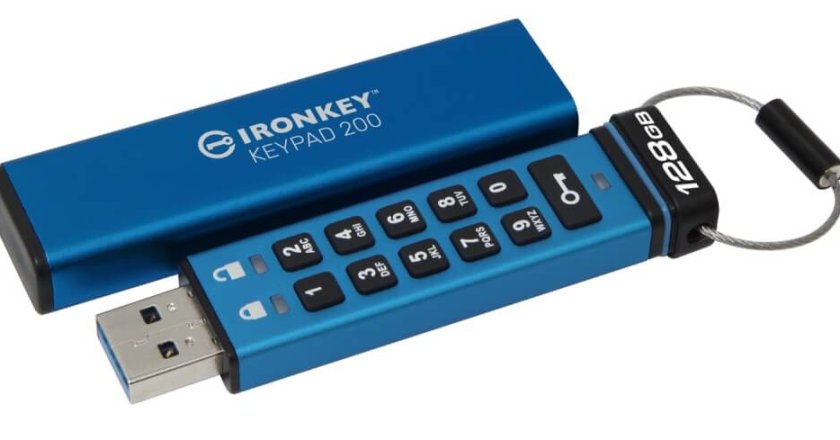
Kingston Announces Hardware-Encrypted IronKey Keypad 200 USB Drive.

(A10 Networks): Understanding and Preventing the Log4j Exploit and Botnets.

ESET Research jointly presents Industroyer2 at Black Hat USA with Ukrainian government representative.