The vulnerability was reported Thursday to Oracle along with proof-of-concept (PoC) exploit code.
The vulnerability was reported Thursday to Oracle along with proof-of-concept (PoC) exploit code.

More and more workers around the world are bringing their personal mobile devices to the office daily, and companies appear to be having trouble keeping up with the trend.

SAP reported revenue growth in the second quarter driven by growth in cloud subscriptions and revenue from support and its HANA in-memory database.

Apple is on the hunt for cloud infrastructure engineers familiar with building large-scale deployments like those at Amazon Web Services and OpenStack companies, according to a job posting.

A new report from the SANS Institute and RSA on help desk security and privacy finds help desk workers are the easiest victims for a determined social engineering criminal.

Despite the significant Java security improvements made by Oracle during the past six months, Java vulnerabilities continue to represent a major security risk for organisations.

Though Kamal Osman Jamjoom (KOJ) Group has not deployed what it believes to be the current number-one solution on the market to boost its HR processes for staff, the company believes that its roll-out of Oracle Fusion will prove a winning move.

Last month, a former CIA technician leaked information on the National Security Agency’s data gathering surveillance programme dubbed PRISM. Joe Lipscombe investigates what relevance this holds for the Middle East.

Cisco is building a router for the Internet of Everything, the company’s initiative to connect the billions of devices – or 99 percent of the world – that it claims isn’t already connected.

The first tools for injecting legitimate Android apps with open-source software that allows an attacker to control an infected smartphone remotely have been found in the criminal underground.
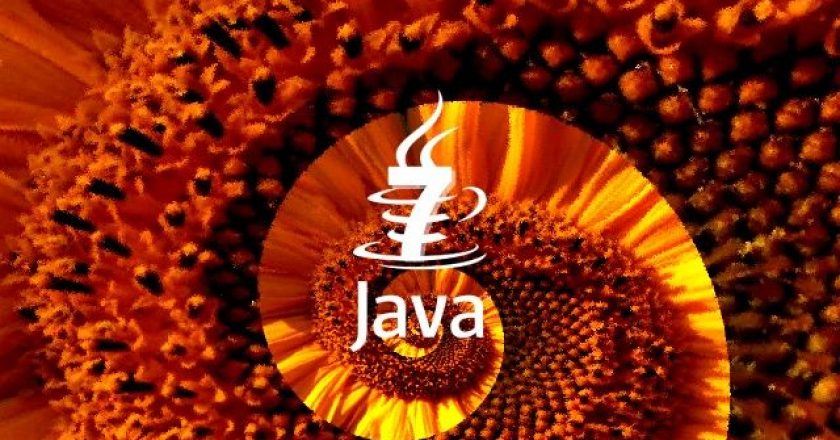
In an odd bit of doublespeak, Microsoft has released a version of its Outlook Web App (OWA) as a native application for the Apple iPhone and iPad.

Can you maintain cost leadership, service levels, solution quality, and deliver projects flexibly and to schedule? You’re worth your weight in gold, no doubt.

Swiss structured cabling specialist R&M has warned Middle East organisations against premature investments as long as standards are not defined and components are not fully developed.

Microsoft has detailed the next software update to its Windows Phone 8 mobile operating system.

Oracle is introducing a new generation of its Exalytics appliance for high-speed data analysis that comes with a slightly higher price tag but major increases in memory and storage capacity.
With margins for traditional commodity gear at all-time low, partners are looking to the peripherals market to make up on lost revenue.

High-growth countries are usually exhibited by a low per capita income. The upside, though, is that such countries, usually emerging countries, are able to do more with fewer resources.
The number of mobile malware apps has jumped 614 percent in the last year, according to studies conducted by McAfee and Juniper Networks.
CommScope has acquired Redwood Systems, which specialises in LED lighting solutions and integrated sensor networks for data centres and buildings, in a bid to deal with growing demands for full-scale intelligent infrastructure solutions.

A second vulnerability that can be exploited to modify legitimate Android apps without breaking their digital signatures has been identified and publicly documented.