Data at rest has long been protected by technology called public key infrastructure (PKI), in which data is encrypted when …


Data at rest has long been protected by technology called public key infrastructure (PKI), in which data is encrypted when …

Proponents of a common scheme for managing user identity in cloud-based applications will pitch their idea to the Internet’s premier standards-setting body …

Emitac Enterprise Solutions today announced that it has achieved Symantec specialisations in the areas of Data Protection and Archiving and …

Extreme Networks this week is rolling out Ethernet switches and a network management application designed to address the BYOD phenomenon at enterprise campuses. Extreme’s Intelligent Mobile …

IBM has taken the secure USB stick concept to its logical extreme, announcing a pilot service capable of streaming an …

Many companies in the Middle East are missing out by not gaining valuable intelligence from threats. Security information and event …

Brocade this week is looking to simplify the campus edge with two additions to its ICX switch line and plans …
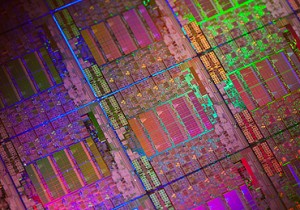
Intel on Tuesday announced the Xeon E5-2600 processors for 2- and 4-socket servers, which is the company’s first major chip …

IT security and data protection company Sophos, and Egnyte, a leading provider of hybrid cloud file server solutions,have announced the integration of …

Extreme Networks this week is rolling out Ethernet switches and a network management application designed to address the BYOD phenomenon at enterprise campuses. Extreme’s Intelligent Mobile …

ICT Roadmap 2012 today brought together leading IT professionals to discuss the top trends and issues affecting enterprises in the …

Implementation of cloud services will create 14 million jobs internationally by 2014, with the greatest increases occurring in emerging markets, …

IT departments must build private clouds for critical applications to provide employees with the benefits of rapid provisioning and pay-as-you-go …

The networking giant is on the road to recovery, thanks to a business model realignment and expenses cut. At the …

Established vendors such as HTC, Sony and LG Electronics want to set their smartphones apart from less expensive devices from …

Despite security and IT integration problems related to the consumerisation of IT in the workplace, CEOs and IT execs are …

Brian Fitzgerald, VP of marketing at RSA, says the security breach at the security company last March was the biggest …

Information risk in the Middle East is very basic and companies in the region are leaving themselves vulnerable to attack. …

RSA used its notorious security breach of last March to its advantage to make the company stronger and closer as …

ManageEngine, makers of a suite of network, systems, applications, and security management software solutions, has announced the integration of Desktop Central and ServiceDesk …