The Most Common Root Causes of Attacks Were Unpatched Vulnerabilities and Compromised Credentials, While Ransomware Continues to Be the Most Common “End Game”.


The Most Common Root Causes of Attacks Were Unpatched Vulnerabilities and Compromised Credentials, While Ransomware Continues to Be the Most Common “End Game”.

The HUAWEI WATCH Ultimate embodies the pinnacle of technology and design innovation among Huawei’s wearables, while the HUAWEI FreeBuds 5 boasts Seamless Curves for Optimal Fit, Ultra Magnetic Driver with Punchy Bass and more.

The Cyber Emergency Readiness Team for Operational Technology marks its first year with over 900 members from more than 50 countries.

Veeam’s growth fuelled by industry leading innovation and strong, trusted relationships with customers, partners and alliances.

GEM’s increased investment commitment comes after Everdome has drawn down the majority of GEM’s initial investment commitment of $10M.

With this partnership, Omnix resellers and customers will get access to engineering solutions with thirty years of embedded best practices while SPIDTECH gets access to regional market with tallest and largest super structures.

CNME Editor Mark Forker spoke to Wassim Berro, Co-Founder of AI start-up Burger Index, to learn more about how the …

Stephan Meyer, CPO, tells Anita Joseph why the DICOTA brand is so popular and how the company focuses on sustainability …

Sam Tayan, Head of METAP at Zoom explains how interpersonal interactions, workflows, and communication channels between workers, teams, and customers …

Nozomi Networks further extends market reach and service delivery options with Vantage now available for purchase in AWS Marketplace.

Infoblox rebrand initiatives reflect confidence and business focus, positioning its critical role in securing the networks of some of the world’s largest companies, appealing to both networking and security professionals alike.

62% of businesses prefer a Unified AI- and ML-powered observability solution to provide a better customer experience.

Over 56% of the core routers ESET purchased from secondary market vendors contained a treasure trove of sensitive data, including corporate credentials, VPN details, cryptographic keys, and more.

Gaurav Mohan, VP, SAARC & Middle East, NETSCOUT highlights that to become an unstoppable enterprise, organizations must consider five essential …

Bybit, the world’s third most visited crypto exchange with 15 million users worldwide, announced the grand opening of its global headquarters in Dubai today.

Chady Smayra and Diana Dib, partners with Strategy & Middle East, part of the PwC network, discuss how the GCC …

Scalability, operational simplicity, and sustainability – with zero compromises.
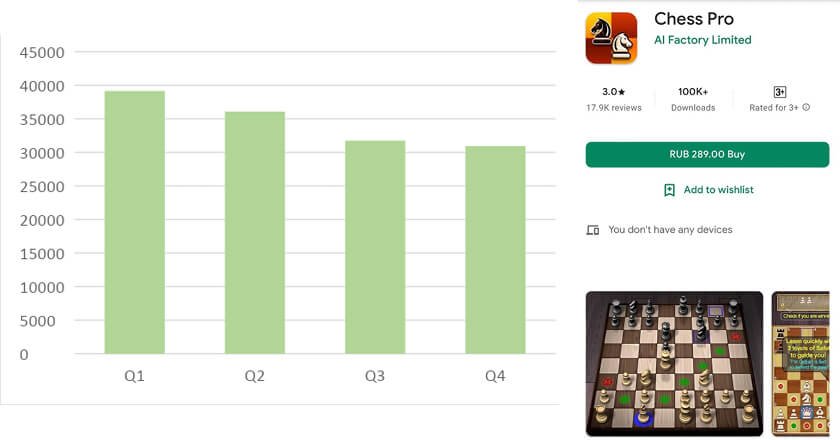
Kaspersky cybersecurity experts have discovered that chess players have been targeted by a range of different attacks from cybercriminals spreading malicious or unwanted mobile programs 一 even on Google Play 一 and Trojans and ransomware disguised as chess applications.

CNME Editor Mark Forker spoke to Reem Asaad, Vice President – Middle East & Africa, at Cisco, to find out …

In moving from chief technology evangelist to CTO, Asanka Abeysinghe will lead the external architecture strategy for WSO2’s open-source and SaaS solutions, which enable software development teams to securely deliver consumer-driven applications.