Apple on Sunday addressed a multi-day outage afflicting its developer site, acknowledging that its systems were hacked.


Apple on Sunday addressed a multi-day outage afflicting its developer site, acknowledging that its systems were hacked.
Comguard recently ran a series of special training workshops for both channel partners and end-users on gateprotect Next Generation Firewalls across the region.

Millions of mobile phones may be vulnerable to spying due to the use of outdated, 1970s-era cryptography, according to new research due to be presented at the Black Hat security conference.
Given the record number of attendees at this year’s Reseller Middle East Partner Excellence Conference, it was clear that the region’s channel players wanted to hear how to tackle new challenges.

The Foreign Intelligence Surveillance Court has renewed permission to the US government for a controversial programme to collect telephone metadata in bulk.

WatchGuard Technologies has been awarded a “Performance Verified Certification” by independent test lab, Miercom, for performing nearly 3.5 times faster …

Wall Street played its own version of war games on Thursday, testing its defences against simulated cyber-attacks bent on taking down US stock exchanges.
The vulnerability was reported Thursday to Oracle along with proof-of-concept (PoC) exploit code.

More and more workers around the world are bringing their personal mobile devices to the office daily, and companies appear to be having trouble keeping up with the trend.
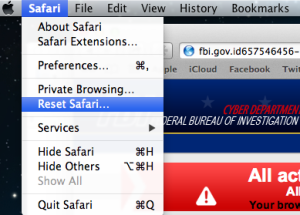
Ransom attackers have finally made the jump from Windows to the Mac with news of a stunningly simple hack that tries to trick browser users into paying a $300 (£200) fine using a simple JavaScript routine.

New research has shown that the vast majority of businesses are exposing sensitive corporate data to cyber-criminals by failing to implement effective BYOD strategies.

A new report from the SANS Institute and RSA on help desk security and privacy finds help desk workers are the easiest victims for a determined social engineering criminal.

Despite the significant Java security improvements made by Oracle during the past six months, Java vulnerabilities continue to represent a major security risk for organisations.

Last month, a former CIA technician leaked information on the National Security Agency’s data gathering surveillance programme dubbed PRISM. Joe Lipscombe investigates what relevance this holds for the Middle East.
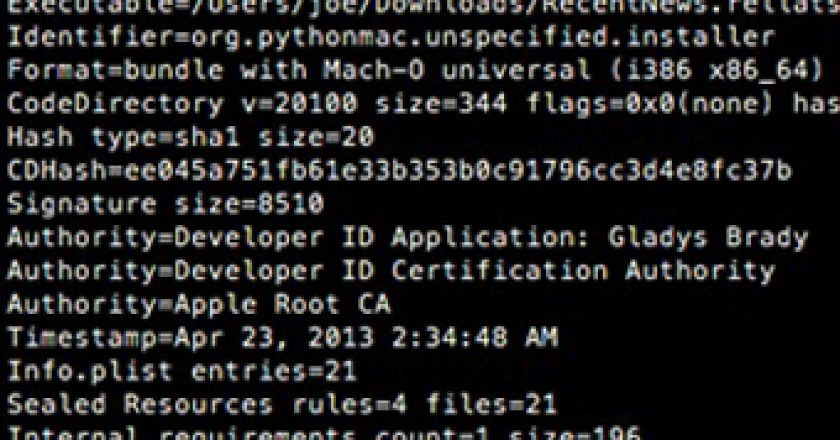
Researchers at F-Secure have discovered malware targeting OS X, which leverages a technique called right-to-left override (RLO) in order to spoof its malicious nature.

The first tools for injecting legitimate Android apps with open-source software that allows an attacker to control an infected smartphone remotely have been found in the criminal underground.

Sufian Dweik, Regional Director, MEMA, Brocade Communications, offers a flexible, on-demand strategy for Middle East enterprises.

A new version of a file-infecting malware program that’s being distributed through drive-by download attacks is also capable of stealing FTP (File Transfer Protocol) credentials.

Symantec has discovered a bizarre ransom Trojan that eschews the usual demand for payment in favour of asking its victims to fill in an online survey to get an unlock code.
According to IDC, Middle East IT spending in 2013 is projected to cross the $32 billion mark which is double the global average.