The website of a U.S. organization specializing in national and international security policy was compromised with malware that targeted a previously unknown vulnerability in Internet Explorer.


The website of a U.S. organization specializing in national and international security policy was compromised with malware that targeted a previously unknown vulnerability in Internet Explorer.

Security researchers have uncovered two unpatched vulnerabilities in Internet Explorer (IE) which have been exploited by attackers in an unusual “watering hole” campaign launched from a U.S.-based website that specialises in domestic and international security policy.

Apple’s latest operating system update, OS X 10.9 Mavericks, is out. If you own a Mac that supports the OS update, you should get it. Now. You certainly can’t beat the price: free!

It doesn’t represent the UI overhaul that iOS 7 did on the mobile side, but it continues to refine OS X, applying polish where needed.

Remember where you were this day; for it will go down in history as the date when LG’s mobile devices began to slightly bend for no demonstrably necessary reason.
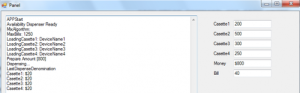
A malicious software program found in ATMs in Mexico has been improved and translated into English, which suggests it may be used elsewhere, according to security vendor Symantec.

Before I dig in, allow me to preface the following with this: I am a photo dabbler. As such, …

Apple doesn’t promote enterprise features in its products, instead choosing to be seen as the consumer’s champion-but this doesn’t mean it doesn’t have any.

A malicious software tool perhaps most famously used to hack RSA’s SecurID infrastructure is still being used in targeted attacks, …

YouTube is adding some new video-playing functions to its mobile app on both iOS and Android devices. Some of the …

One of the most anticipated smartphones of the year, Motorola’s flagship Moto X, is finally here, and it’s said to be one of the most customisable phone ever built.

F5 Networks says its BIG-IP 10200v with Advanced Firewall Manager (AFM) can handle traffic at 80-Gbps rates while screening and protecting tens of millions of connections, and simultaneously load-balancing server traffic.

A number of new capabilities, plus enhancements to existing ones, promise to make Windows Server 2012 R2 an even stronger candidate for the majority of virtualisation tasks most organisations need to support.

The source code for the Carberp banking Trojan program is being offered for sale on the underground market at a very affordable price.

Hackers have found a devious new way to disseminate malware: They’re using peer-to-peer networks.

Security researchers have identified multiple samples of the recently discovered “KitM” spyware for Mac OS X, including one dating back …

While much of the hype for software-defined networking is focused on large-scale data centre deployments, some companies are taking a …
According to BlackBerry representatives, 80% to 90% of BlackBerry’s 76 million subscribers are still using older BlackBerry smartphones with physical …

Researchers following a cyber espionage campaign apparently bent on stealing drone-related technology secrets have found additional malware related to the …

Recent massive cyber attacks that paralysed computer networks at several South Korean banks and broadcasters, strongly suspected to have been …