Security researchers said they’ve spotted a new type of banking malware that rivals the capabilities of the infamous Zeus malware. …
Security researchers said they’ve spotted a new type of banking malware that rivals the capabilities of the infamous Zeus malware. …

A suspected Iranian hacker group seeded Facebook and LinkedIn with bogus profiles of women and created a fake online news organisation to get digitally closer to more than 2,000 people whom it wanted to spy on.

A suspected Iran-based hacking group known for defacing websites has shown increased ambition over the past few months, targeting U.S. defense contractors and Iranian dissidents, according to a new report from security company FireEye.

Hitachi Data Systems has announced ‘Continuous Cloud Infrastructure’, consisting of its Storage Virtualisation Operating System (SVOS), Virtual Storage Platform G1000 (VSP G1000), a new version of the Hitachi Command Suite management platform and enhancements to its Unified Compute Platform converged computing offerings.

Microsoft has unveiled Cortana, its response to Apple’s Siri and Google’s Now, as it seeks to make its Windows Phone OS a stronger competitor to iOS and Android.

Security researchers at ESET, in collaboration with CERT-Bund, the Swedish National Infrastructure for Computing as well as other agencies, have uncovered a widespread cybercriminal campaign that has seized control of over 25,000 Unix servers worldwide.

Experts say it takes time, training and collaboration to thwart APTs. But with these best practices, you can keep your defenses high.
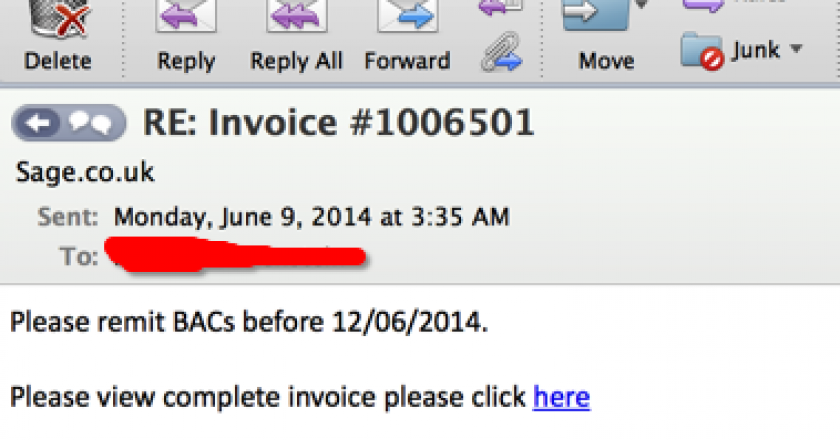
Intel has released a new tool for remotely managing servers from multiple hardware vendors, though wary of upsetting partners as it looks to make more money from software.

2014 marks the 10th anniversary of Cabir, the world’s first mobile phone malware. To mark this occasion, Fortinet’s FortiGuard Labs is taking a stroll down memory lane to examine the evolution and significance of mobile threats during the last 10 years.

U.S. President Barack Obama has nominated an expert cryptologist to head the National Security Agency at a time when the agency is under pressure to reform its surveillance.
SDN is a technology that promises to be the next big thing not only for IT organisations and networking vendors, but also for service providers, says Muhammad Rehan Sami, Senior Solution Architect, Business, Etisalat

Palo Alto Networks has announced enhancements to its enterprise security platform WildFire.

Kaspersky Lab has recorded thousands of attempts to infect computers used for online banking with a malicious program that its creators claim can attack “any bank in any country”.
A team of malware developers is preparing to sell a new ransomware programme that encrypts files on infected computers, according to a volunteer group of security researchers who tracked the development of the threat on underground forums in recent weeks.

New attack campaigns have infected point-of-sale (PoS) systems around the world with sophisticated malware designed to steal payment card and transaction data.

Thirteen people, including the creator of Blackhole, a popular exploit tool used to infect computers with malware, were arrested and charged in Russia with creating and participating in a criminal organisation.

A security researcher has released software and technical instructions for modifying a drone so that it can identify and hijack other drones.
Researchers have demonstrated that microphones and speakers built into laptops can be used to covertly transmit and receive data through inaudible audio signals.

Two million logins and passwords from services such as Facebook, Google and Twitter have been found on a Netherlands-based server, part of a large botnet using controller software nicknamed “Pony.”
Cybercriminals are increasingly using the “Blackshades” malware program whose source code was leaked three years ago, according to an analysis by Symantec.