In August 2024, Proofpoint researchers identified an unusual campaign using a novel attack chain to deliver custom malware. The threat actor named the malware “Voldemort” based on internal filenames and strings used in the malware.
The attack chain comprises multiple techniques currently popular within the threat landscape as well as uncommon methods for command and control (C2), like the use of Google Sheets. Its combination of tactics, techniques, and procedures (TTPs), lure themes impersonating government agencies of various countries, and odd file naming and passwords like “test” are notable. Researchers initially suspected the activity may be a red team. However, the large volume of messages and analysis of the malware very quickly indicated it was a threat actor.
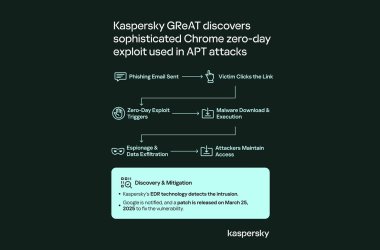
Proofpoint assesses with moderate confidence this is likely an advanced persistent threat (APT) actor with the objective of intelligence gathering. However, Proofpoint does not have enough data to attribute with high confidence to a specific named threat actor (TA). Despite the widespread targeting and characteristics more typically aligned with cybercriminal activity, the nature of the activity and capabilities of the malware show more interest in espionage rather than financial gain at this time.
Voldemort is a custom backdoor written in C. It has capabilities for information gathering and to drop additional payloads. Proofpoint observed Cobalt Strike hosted on the actor’s infrastructure, and it is likely that is one of the payloads that would be delivered.
Beginning on 5 August 2024, the malicious activity included over 20,000 messages impacting over 70 organizations globally. The first wave of messages included a few hundred daily but then spiked on 17 August with nearly 6,000 total messages.
Messages purported to be from various tax authorities notifying recipients about changes to their tax filings. Throughout the campaign, the actor impersonated tax agencies in the U.S. (Internal Revenue Service), the UK (HM Revenue & Customs), France (Direction Générale des Finances Publiques), Germany (Bundeszentralamt für Steuern), Italy (Agenzia delle Entrate), and from August 19, also India (Income Tax Department), and Japan (National Tax Agency). Each lure was customised and written in the language of the authority being impersonated.
Proofpoint analysts correlated the language of the email with public information available on a select number of targets, finding that the threat actor targeted the intended victims with their country of residence rather than the country that the targeted organisation operates in or country or language that could be extracted from the email address. For example, certain targets in a multi-national European organisation received emails impersonating the IRS because their publicly available information linked them to the US. In some cases, it appears that the threat actor mixed up the country of residence for some victims when the target had the same (but uncommon) name as a more well-known person with a more public presence. Emails were sent from suspected compromised domains, with the actor including the agency’s real domain in the email address.
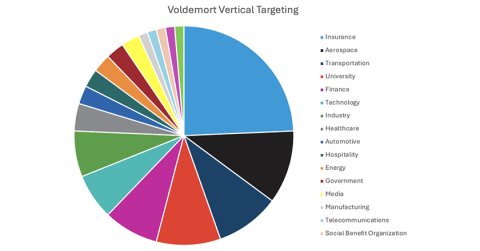
The threat actor targeted 18 different verticals, but nearly a quarter of the organisations targeted were insurance companies. Aerospace, transportation, and university entities made up the rest of the top 50% of organisations targeted by the threat actor.
Proofpoint does not attribute this activity to a tracked threat actor. Based on the functionality of the malware and collected data observed when examining the Sheet, information gathering was one objective of this campaign. While many of the campaign characteristics align with cybercriminal threat activity, we assess this is likely espionage activity conducted to support as yet unknown final objectives.
The Frankensteinian amalgamation of clever and sophisticated capabilities, paired with very basic techniques and functionality, makes it difficult to assess the level of the threat actor’s capability and determine with high confidence the ultimate goals of the campaign. It is possible that large numbers of emails could be used to obscure a smaller set of actual targets, but it’s equally possible the actors wanted to genuinely infect dozens of organisations. It is also possible that multiple threat actors with varying levels of experience in developing tooling and initial access worked on this activity. Overall, it stands out as an unusual campaign.
The behaviour combines a variety of recently popular techniques observed in several disparate campaigns from multiple cybercriminal threat actors that have used similar techniques as part of ongoing experimentation across the initial access ecosystem. Many of the techniques used in the campaign are observed more frequently in the cybercriminal landscape, demonstrating that actors engaging in suspected espionage activity often use the same TTPs as financially motivated threat actors.
While the activity appears to align with espionage activity, it is possible that future activities associated with this threat cluster may change this assessment. In that case, it would indicate cybercriminal actors, while demonstrating some typical e-crime delivery characteristics, used customised malware with unusual features currently only available to the operators and not abused in widespread campaigns, as well as very specific targeting not normally seen in financially motivated campaigns.
Defense against observed behaviors includes restricting access to external file sharing services to only known, safelisted servers; blocking network connections to TryCloudflare if it is not required for business purposes; and monitoring and alerting on use of search-ms in scripts and suspicious follow-on activity such as LNK and PowerShell execution.
Proofpoint reached out to our industry colleagues about the activities in this report abusing their services, and their collaboration is appreciated.
Image Credit: Proofpoint