Infoblox has recently released new research that unveils critical insights into the cybercriminal entity VexTrio, exposing its complex network of malicious connections with other cybercriminal enterprises, such as ClearFake and SocGholish.
This work, done in collaboration with the security researcher who discovered the ClearFake malware, aims to reveal the depth of these threat actors’ affiliations and expose their illicit activities that have also been detected within networks globally.
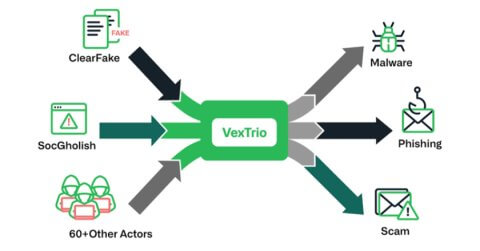
VexTrio controls a large and malicious network that reaches a wide audience of internet users. Through a criminal affiliate program with over 60 partners, including high-profile entities like SocGholish and ClearFake – it stands out as the most pervasive DNS threat actor, operating for six years and impacting over 50% of customer networks. Its role as an invisible traffic broker has kept it undetected by other vendors, complicating detection and tracking.
Infoblox’s research has also generated a number of other major findings. In particular:
- VexTrio operates their affiliate program in a unique way, providing a small number of dedicated servers to each affiliate.
- VexTrio’s affiliate relationships appear longstanding. For example, SocGholish has been a VexTrio affiliate since at least April 2022. While less total time, we assess ClearFake has worked with VexTrio throughout its lifetime; at least since launching their campaigns in August 2023.
- VexTrio attack chains can include multiple actors. We have observed four actors in an attack sequence.
- VexTrio and its affiliates are abusing referral programs related to McAfee and Benaughty.
- VexTrio controls multiple TDS networks, which function in different ways. In particular, we reveal a new DNS-based TDS first observed in late-December 2023.
Infoblox has been tracking VexTrio via DNS since 2020, but new evidence shows their enterprise began in 2017, possibly earlier. The ongoing evolution of VexTrio, coupled with its partnership with significant actors like SocGholish, highlights its crucial role in the criminal industry, contributing to the industry’s lack of recognition.
VexTrio’s affiliate program operates similarly to a legitimate marketing affiliate network. Each cyberattack uses DNS infrastructure owned by multiple cybercriminal entities. Participating cybercriminal affiliates will forward user traffic originating from their own services (such as a compromised website) to VexTrio-controlled TDS servers. Subsequently, VexTrio relays these flows of user traffic to other cybercriminal affiliate networks or fake web pages. In many cases, VexTrio also redirects victims to their ongoing phishing campaigns.
While SocGholish and ClearFake are most associated with malware and fake software update pages, these two entities operate TDS servers to route internet users based on their details – device information, operating system, location, and other personal details.
The research underscores the critical role of TDS in the estimated $8 trillion cybercrime economy. Globally, the cost of cybercrime is estimated at over US$7 trillion and is expected to grow steadily over the years. In the Asia-Pacific region, the rapid pace of digitalisation and the accelerated adoption of new technologies have made it one of the major hotspots for cybercrime.
Read the full breakdown of Infoblox’s findings here.





