Stuart Collingwood, General Manager UK & Europe at Owl labs, on why the partnership is a game changer for the video collaboration industry in the region.


Stuart Collingwood, General Manager UK & Europe at Owl labs, on why the partnership is a game changer for the video collaboration industry in the region.

It is down to the CIO to ensure that an organisation can harness the benefits of modern tools and methods without creating needless complication or an environment they can no longer effectively govern.
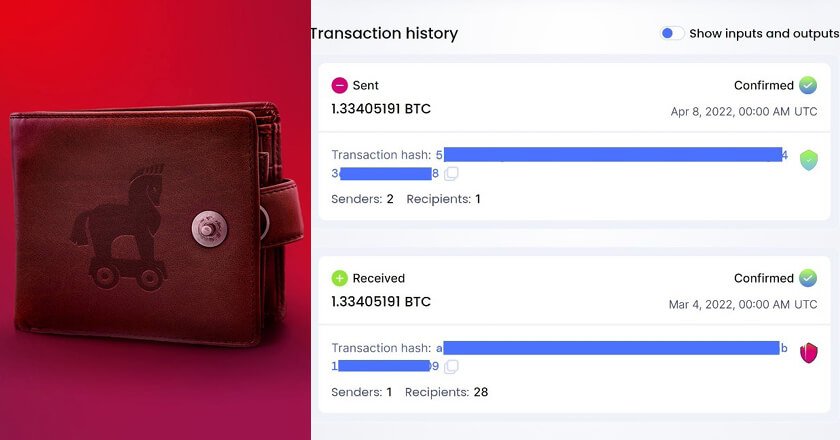
Kaspersky shared the details behind the incident of cryptocurrency theft involving a hardware wallet, which resulted in the loss of 1.33 BTC worth $29,585.

Stephen Gill, Academic Head of the School of Mathematical and Computer Sciences, Heriot-Watt University Dubai, assesses the benefits and challenges of AI use in education.

Vinay Sharma, Director of IT at Gulftainer, outlines how the company took a ‘holistic approach’ to developing their multi-cloud strategy in a bid to effectively transform their day-to-day operations.

It can be said that ESG and GRC are both critical for business success. Integrating the GRC into ESG goals will reduce costs and boost productivity.

Artificial intelligence moves systems towards human type decision making, while machine language churns data rapidly looking for patterns, improving the capability to block any threat actor.

Cisco Talos has released its cybersecurity report for the first quarter of 2023, highlighting the most common attacks, targets and …

Samantha Rowles, Operations Director for Transport at Serco Middle East, has called the strategy being rolled out by RTA as …
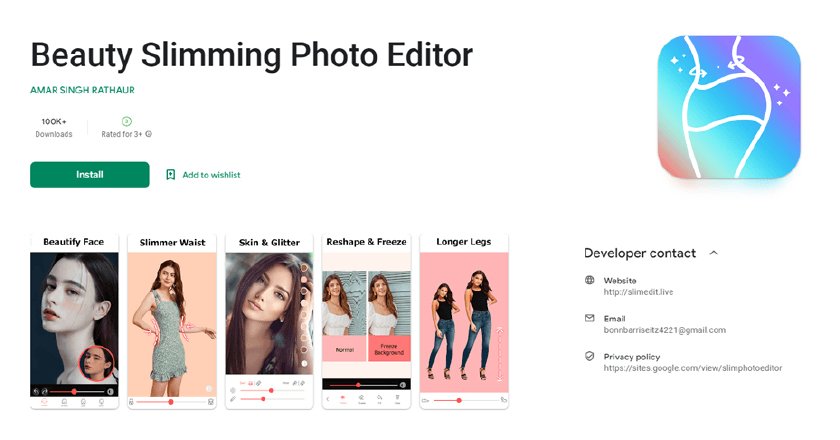
The new Trojan family, Fleckpe, is Kaspersky’s latest discovery that spreads via Google Play under the guise of photo editors, wallpaper packs and other apps. In fact, it subscribes the unwitting user to paid services.

Nozomi Networks Delivers Industry’s First AI-powered Cybersecurity Analysis and Response Engine for Critical Infrastructure.
CNME Editor Mark Forker speaks to SolarWinds CEO Sudhakar Ramakrishna, on his leadership style, the challenge of staying relevant, removing …
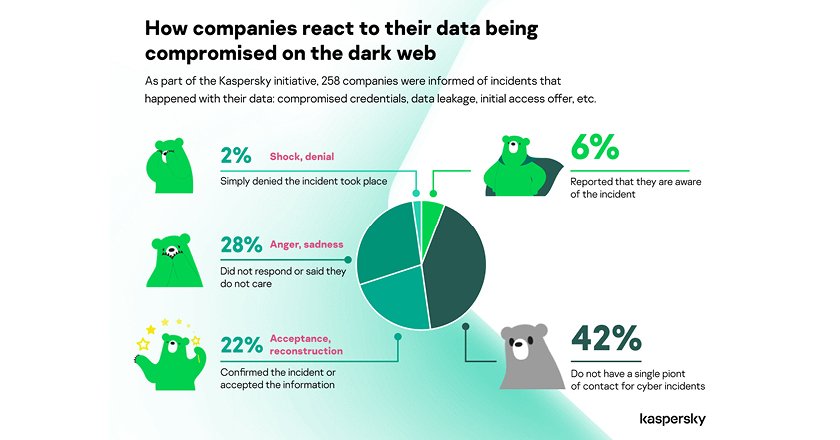
When detecting a cybersecurity incident related to corporate data compromised on the Dark web, whether it be sale of a database, infrastructure compromise or ransomware, the victim company was notified about this threat by Kaspersky team.

Mark Forker, spoke to K.S. Parag, FVC, and Nicolas Bliaux, Jabra, to discuss their recently announced distribution partnership and how this will change the landscape of intelligent video solutions going forward.